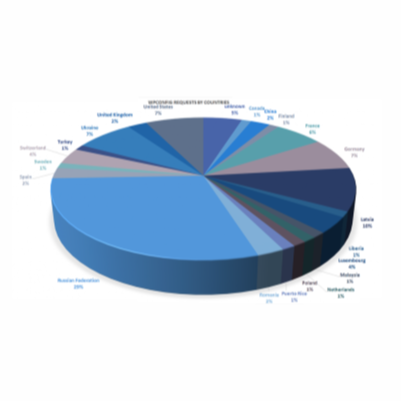
CompSec Direct’s president presents Shodan research at local security conference in Puerto Rico
CompSec Direct president, Jose Fernandez, presented an open-source intelligence gathering tool called Shodan-Runner at the Bsides PR security conference hosted on Oct 6,2016 in Puerto Rico. The tool allows users to use external CSV files in conjunction with the Shodan api in python to search for associations between different different fields. Using this tool reduces initial [...]